A Torrent is a peer-to-peer technology that uses small files containing information about a specific (usually large) file. This information is about the users having the file, and essentially plays the role of liaison between users. The size of torrent files is very small and has an extension of .torrent. The protocol used to exchange files, is the BitTorrent protocol. Basically we are sharing files that are not in a central server, but rather on the computers of other users. What is important to stress out here is that when we download a file we also upload it the same time (if there is a demand for this file).
Torrent Clients
Torrent clients are the programs we use to connect with other users and to manage the torrents. There are several different options. The most popular (free) torrent client programs are:
uTorrent (www.utorrent.com)
This is a very light client that does not even need installation (although there is also a version that you can install) with several features. Recently has become very popular as a client and has also introduced a public beta version of uTorrent WebUI, which allows users to control downloads from any computer.
Azureus (http://azureus.sourceforge.net)
It is a powerful client with great potential and a very large set of parameters. You need java installed to work and is very popular. The disadvantage of this client is that its too heavy as a program.
BitComet (http://www.bitcomet.com)
It is a very powerful and light client. It is built in C++ and incorporates a browser as well. It is considered to be very quick in downloading.
Where do I find Torrents
Torrents can be found at various sites offering such content. Usually these site are called trackers and are either open to everyone (which reduces the credibility of their content) or closed (communities) with limited members. In the second case, usually the content is more remarkable and trusted, while the speeds achieved are also better. For example I would mention only one tracker, the linuxtracker.org, where you can find open-source software, Linux distributions, etc.
Torrent Terminology
Seeders
These are users who have in their possession the entire file which we want to download, and they make the file available to others.
Leechers
These are users not having in their possession the entire file but part of it and are in the process of downloading.
Please note here that when someone is a leecher, and downloads a file, then at the some time he also uploads the file to other leechers interested for the particular file.
Ratio
The ratio is a number that comes out of the division of the Mbytes that the user has uploaded divided by the Mbytes that the user has downloaded. So if a user has uploaded to the community a total of 1.8 GB and has downloaded 3 GB, then he has a ratio of 1.8 / 3 = 0.6. From the above we can get the golden rule of torrents, that for each file we download, we must hold it (seed it) at least until its ratio becomes 1 so that we offer to the community as much as we received.
Some communities have rules on the ratio of users and there are several «punishments» for low ratio, such as getting banned from the site, lower speeds and / or major delays. Open torrent sites usually do not have such restrictions.
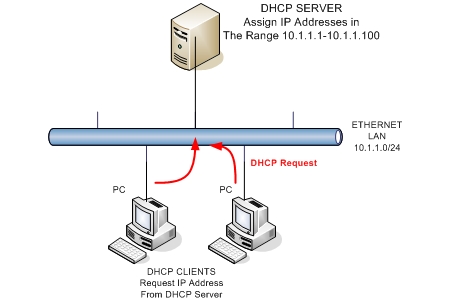
How does Trackers Work
Let us see into more detail of how trackers work.
A tracker hosts only the files ending in .torrent, not the files that are being downloaded. These files exist only on the computers of users. The process of communication is as follows. The A user visits a tracker and selects among the many available records a file to download, lets say the ubuntu.iso. He requests the tracker to obtain the .torrent file which describes ubuntu.iso. From the torrent file, user A learns that users B and C have the whole ubuntu.iso file and that user D has only 25% of the file. Now is the turn of the client (e.g of utorrent) to do its job. The program sends requests to users B, C and D for ubuntu.iso, and once the clients of these users respond, the transfer of the file begins.